Cryptographic Algorithms: Symmetric Encryption Principles
Introduction
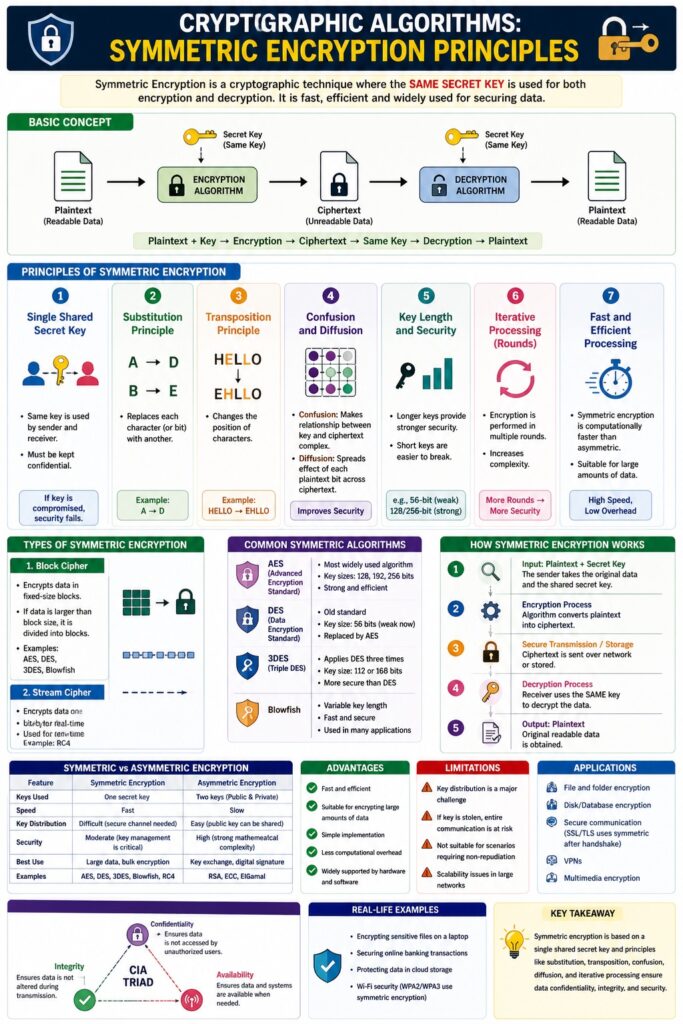
Symmetric Encryption is a cryptographic technique where the same secret key is used for both encryption and decryption.
👉 “One key locks and unlocks the data.”
It is one of the oldest and fastest encryption methods, widely used for securing data in storage and communication.
Basic Concept
In symmetric encryption:
- Plaintext → Original readable data
- Encryption Algorithm → Converts plaintext into cipher text
- Secret Key → Used for both encryption and decryption
- Ciphertext → Encrypted unreadable data
Plaintext + Key → Encryption → Ciphertext
Ciphertext + Same Key → Decryption → Plaintext
Principles of Symmetric Encryption
1. Single Shared Secret Key
Explanation
- Same key is used by sender and receiver
- Must be kept confidential
📌 If key is compromised → system security fails
2. Substitution Principle
Explanation
- Replaces characters with other characters
📌 Example: A → D
3. Transposition Principle
Explanation
- Rearranges positions of characters
📌 Example: HELLO → EHLLO
4. Confusion and Diffusion
Confusion
- Makes relationship between key and ciphertext complex
Diffusion
- Spreads influence of each plaintext bit across ciphertext
📌 Improves security
5. Key Length and Security
Explanation
- Longer keys → stronger security
- Short keys → easier to break
📌 Example:
- 56-bit (weak)
- 128/256-bit (strong)
6. Iterative Processing (Rounds)
Explanation
- Encryption performed in multiple rounds
📌 Increases complexity
7. Fast and Efficient Processing
Explanation
- Symmetric encryption is faster than asymmetric
📌 Suitable for large data
Types of Symmetric Encryption
1. Block Cipher
Description
- Encrypts data in fixed-size blocks
Examples
- AES
- DES
2. Stream Cipher
Description
- Encrypts data one bit/byte at a time
Examples
- RC4
Common Symmetric Algorithms
- AES (Advanced Encryption Standard)
- DES (Data Encryption Standard)
- 3DES (Triple DES)
- Blowfish
Advantages of Symmetric Encryption
- Fast and efficient
- Suitable for large data
- Simple implementation
Limitations
- Key distribution problem
- Less secure for communication if key is shared insecurely
- Scalability issues
Symmetric vs Asymmetric Encryption
| Feature | Symmetric | Asymmetric |
|---|---|---|
| Keys | One key | Two keys |
| Speed | Fast | Slow |
| Security | Moderate | High |
| Use | Data encryption | Key exchange |
Applications of Symmetric Encryption
- File encryption
- Disk encryption
- Secure communication (SSL/TLS uses symmetric after handshake)
- Database security
Symmetric Encryption and CIA Triad
- Confidentiality → Protects data
- Integrity → Ensures secure transmission
- Availability → Fast access
Real-Life Example
- Encrypting files on a computer
- Securing data in banking systems
Conclusion
Symmetric encryption is a fast, efficient, and widely used cryptographic technique based on a shared secret key. Its principles like substitution, transposition, confusion, and diffusion ensure strong security. However, secure key management is critical for its effectiveness.
📘 MCA Exam Tip
For 10–15 marks:
- Definition
- Explain principles (5–7 points)
- Add diagram
- Give examples (AES, DES)
- Mention advantages & limitations