Intrusion Detection – Detailed Explanation
Introduction
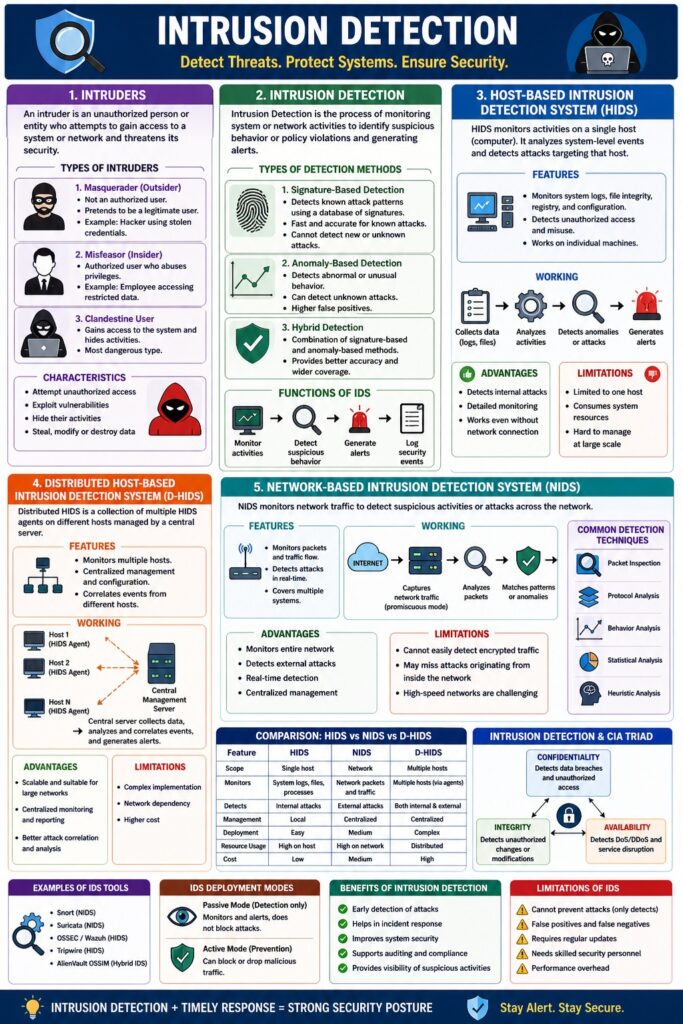
Intrusion Detection is the process of monitoring computer systems and networks to detect unauthorized access, misuse, or attacks.
👉 “Intrusion Detection = Identify suspicious activities in a system/network.”
It plays a vital role in Information Security by helping detect attacks early and respond quickly.
1. Intruders
Definition
An Intruder is a person or entity that tries to gain unauthorized access to a system or network.
Types of Intruders
1. Masquerader (Outsider)
- Unauthorized user pretending to be legitimate
📌 Example: Hacker using stolen credentials
2. Misfeasor (Insider)
- Authorized user misusing privileges
📌 Example: Employee accessing restricted data
3. Clandestine User
- Gains control and hides activities
📌 Most dangerous type
Characteristics of Intruders
- Attempt unauthorized access
- Exploit vulnerabilities
- Hide their activities
- Steal or modify data
2. Intrusion Detection
Definition
Intrusion Detection is the process of:
- Monitoring system activities
- Identifying suspicious behavior
- Alerting administrators
Types of Detection Methods
1. Signature-Based Detection
- Detects known attack patterns
📌 Fast but cannot detect new attacks
2. Anomaly-Based Detection
- Detects abnormal behavior
📌 Can detect unknown attacks
3. Hybrid Detection
- Combination of both methods
Functions of Intrusion Detection System (IDS)
- Monitor system/network activity
- Detect suspicious behavior
- Generate alerts
- Log security events
3. Host-Based Intrusion Detection System (HIDS)
Definition
A Host-Based IDS (HIDS) monitors activities on a single computer (host).
Features
- Monitors system logs
- Tracks file changes
- Detects unauthorized access
- Works on individual machines
Working
- Collects system data (logs, files)
- Analyzes activities
- Detects anomalies or attacks
- Generates alerts
Advantages
- Detects internal attacks
- Detailed system monitoring
- Works even without network
Limitations
- Limited to one host
- Resource consumption
- Difficult to manage at scale
4. Distributed Host-Based Intrusion Detection System (D-HIDS)
Definition
A Distributed HIDS is a system where multiple host-based IDS are connected and managed centrally.
Features
- Monitors multiple hosts
- Centralized control
- Correlates data from different systems
Working
- Each host collects data
- Data sent to central server
- Central system analyzes patterns
- Alerts generated for threats
Advantages
- Scalable
- Better attack detection
- Centralized monitoring
Limitations
- Complex setup
- Network dependency
- Higher cost
5. Network-Based Intrusion Detection System (NIDS)
Definition
A Network-Based IDS (NIDS) monitors network traffic to detect suspicious activities.
Features
- Monitors packets in network
- Detects attacks in real-time
- Covers multiple systems
Working
- Captures network traffic
- Analyzes packets
- Matches patterns or anomalies
- Generates alerts
Advantages
- Monitors entire network
- Detects external attacks
- Real-time detection
Limitations
- Cannot detect encrypted traffic easily
- May miss internal attacks
- High-speed networks are challenging
Comparison: HIDS vs NIDS vs D-HIDS
| Feature | HIDS | NIDS | D-HIDS |
|---|---|---|---|
| Scope | Single host | Network | Multiple hosts |
| Detection | Internal | External | Both |
| Management | Local | Central | Centralized |
| Complexity | Low | Medium | High |
Intrusion Detection and CIA Triad
- Confidentiality → Detect data breaches
- Integrity → Detect unauthorized changes
- Availability → Detect DoS attacks
Intrusion Detection in Cyber Law (India)
Under IT Act, 2000:
- Section 43 → Unauthorized access
- Section 66 → Cyber offences
📌 IDS helps organizations comply with security regulations.
Real-Life Examples
- Detecting unauthorized login attempts
- Identifying malware activity
- Monitoring suspicious network traffic
Advantages of Intrusion Detection
- Early attack detection
- Improves security
- Helps in incident response
- Supports auditing
Limitations
- False positives
- Requires skilled management
- Cannot prevent attacks (only detects)
Conclusion
Intrusion Detection is a critical security mechanism that helps identify unauthorized activities in systems and networks. By using HIDS, NIDS, and Distributed IDS, organizations can effectively monitor and respond to cyber threats, ensuring better protection of digital assets.
📘 MCA Exam Tip
For 10–15 marks:
- Define intruders
- Explain IDS
- Cover HIDS, NIDS, D-HIDS
- Add comparison table
- Include advantages + limitations