Firewalls – Complete Detailed Explanation (MCA Level)
Introduction
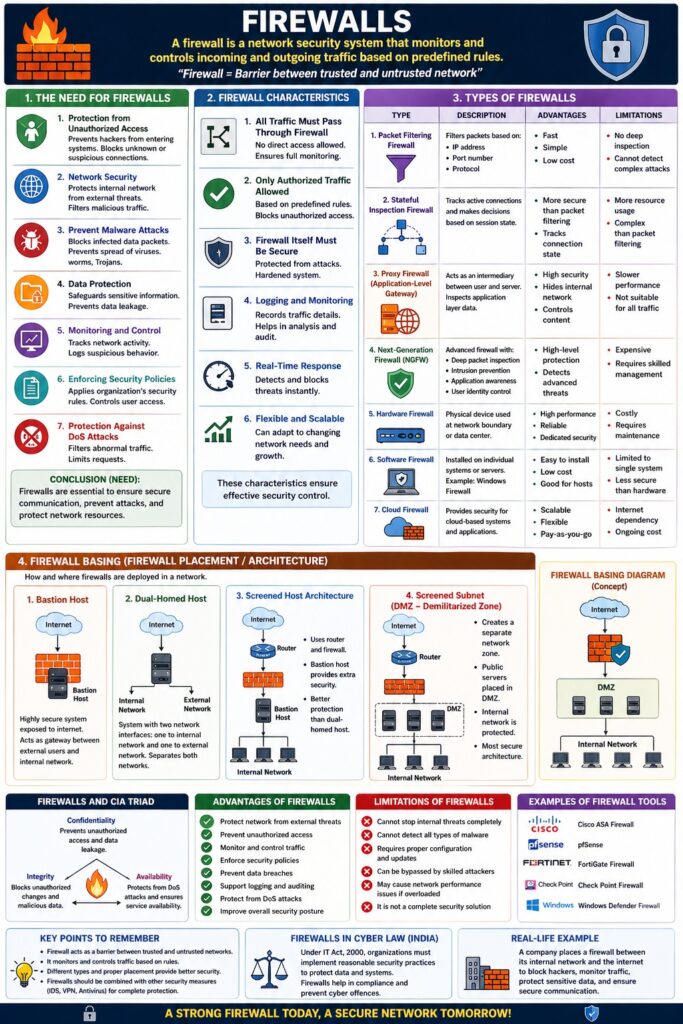
A Firewall is a network security system that monitors and controls incoming and outgoing traffic based on predefined security rules.
👉 “Firewall = Barrier between trusted and untrusted network”
It acts as the first line of defense against cyber threats.
1. The Need for Firewalls
Why Firewalls are Required
1. Protection from Unauthorized Access
- Prevents hackers from entering systems
- Blocks unknown or suspicious connections
2. Network Security
- Protects internal network from external threats
- Filters malicious traffic
3. Prevent Malware Attacks
- Blocks infected data packets
- Prevents spread of viruses, worms, Trojans
4. Data Protection
- Safeguards sensitive information
- Prevents data leakage
5. Monitoring and Control
- Tracks network activity
- Logs suspicious behavior
6. Enforcing Security Policies
- Applies organization’s security rules
- Controls user access
7. Protection Against DoS Attacks
- Filters abnormal traffic
- Limits requests
📌 Conclusion (Need):
Firewalls are essential to ensure secure communication, prevent attacks, and protect network resources.
2. Firewall Characteristics
A good firewall should have the following key characteristics:
1. All Traffic Must Pass Through Firewall
- No direct access allowed
- Ensures full monitoring
2. Only Authorized Traffic Allowed
- Based on predefined rules
- Blocks unauthorized access
3. Firewall Itself Must Be Secure
- Protected from attacks
- Hardened system
4. Logging and Monitoring
- Records traffic details
- Helps in analysis
5. Real-Time Response
- Detects and blocks threats instantly
6. Flexible and Scalable
- Can adapt to changing network needs
📌 These characteristics ensure effective security control.
3. Types of Firewalls
1. Packet Filtering Firewall
Description
- Filters packets based on:
- IP address
- Port number
- Protocol
Advantages
- Fast
- Simple
Limitations
- No deep inspection
2. Stateful Inspection Firewall
Description
- Tracks active connections
- Makes decisions based on session state
Advantages
- More secure than packet filtering
3. Proxy Firewall (Application-Level Gateway)
Description
- Acts as an intermediary between user and server
Advantages
- High security
- Hides internal network
Limitations
- Slower performance
4. Next-Generation Firewall (NGFW)
Description
- Advanced firewall with:
- Deep packet inspection
- Intrusion prevention
- Application awareness
Advantages
- High-level protection
5. Hardware Firewall
Description
- Physical device
- Used in organizations
6. Software Firewall
Description
- Installed on individual systems
📌 Example: Windows Firewall
7. Cloud Firewall
Description
- Provides security for cloud-based systems
4. Firewall Basing (Firewall Placement/Architecture)
Firewall basing refers to how and where firewalls are deployed in a network.
1. Bastion Host
Description
- Highly secure system exposed to internet
📌 Acts as gateway
2. Dual-Homed Host
Description
- System with two network interfaces
- Separates internal and external network
3. Screened Host Architecture
Description
- Uses router + firewall
📌 Provides layered security
4. Screened Subnet (DMZ – Demilitarized Zone)
Description
- Creates a separate network zone
Features
- Public servers placed in DMZ
- Internal network protected
📌 Most secure architecture
Firewall Basing Diagram (Concept)
Internet → Firewall → DMZ → Internal Network
Firewalls and CIA Triad
| CIA Component | Role of Firewall |
|---|---|
| Confidentiality | Prevent unauthorized access |
| Integrity | Block malicious data |
| Availability | Protect from DoS attacks |
Advantages of Firewalls
- Protect network from attacks
- Monitor traffic
- Enforce policies
- Prevent data breaches
Limitations
- Cannot stop internal threats completely
- Cannot detect all malware
- Requires proper configuration
Firewalls and Cyber Law (India)
Under IT Act, 2000:
- Organizations must implement reasonable security practices
- Firewalls help in compliance
Real-Life Example
- Company firewall blocking unauthorized login attempts
- Banking system protecting customer data
Conclusion
Firewalls are essential security tools that act as a protective barrier between networks. By implementing different types and proper basing techniques, organizations can ensure strong network security, data protection, and compliance with cyber laws.
📘 MCA Exam Tip
For 10–15 marks:
- Define firewall
- Explain:
- Need
- Characteristics
- Types
- Firewall basing
- Add diagram (DMZ)
- Write conclusion