Denial-of-Service (DoS) Attacks – Detailed Explanation
Introduction
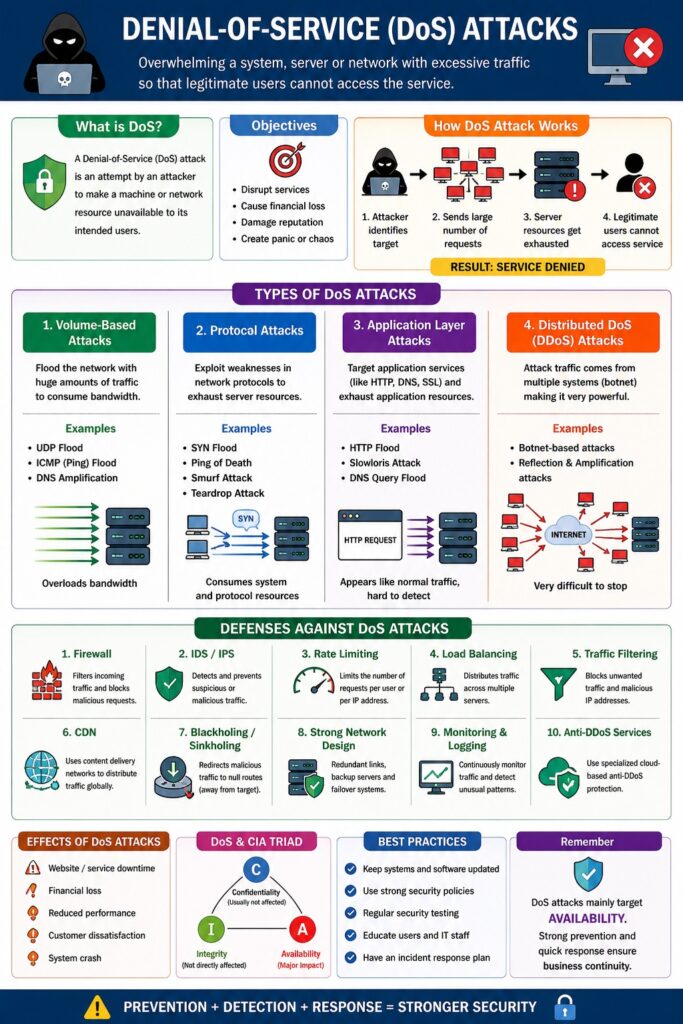
A Denial-of-Service (DoS) attack is a cyber attack in which an attacker attempts to make a system, server, or network unavailable to its intended users by overwhelming it with excessive traffic or requests.
👉 “DoS = Making services unavailable to legitimate users.”
When multiple systems are used for the attack, it is called a Distributed Denial-of-Service (DDoS) attack.
Definition
A DoS attack is:
- An attempt to disrupt normal functioning
- By exhausting system resources
- Resulting in denial of service
Objectives of DoS Attacks
- Disrupt services
- Cause financial loss
- Damage reputation
- Create panic or chaos
Types of DoS Attacks
1. Volume-Based Attacks
Description
Flood the network with massive traffic.
Examples
- UDP Flood
- ICMP (Ping) Flood
📌 Overloads bandwidth
2. Protocol Attacks
Description
Exploit weaknesses in network protocols.
Examples
- SYN Flood
- Ping of Death
- Smurf Attack
📌 Consumes server resources
3. Application Layer Attacks
Description
Target application services (HTTP, DNS).
Examples
- HTTP Flood
- Slowloris attack
📌 Hard to detect (looks like normal traffic)
4. Distributed DoS (DDoS) Attacks
Description
Attack launched from multiple systems (botnet).
📌 Very powerful and difficult to stop
Working of DoS Attack
Step-by-Step Process
- Attacker identifies target
- Sends large number of requests
- Server resources get exhausted
- Legitimate users cannot access service
Attack Traffic → Server Overload → Resource Exhaustion → Service Denied
Effects of DoS Attacks
- Website downtime
- Loss of business revenue
- Reduced performance
- Customer dissatisfaction
- System crash
Examples of DoS Attacks
- Website crash during heavy traffic attack
- Online banking service disruption
- E-commerce site unavailable during sale
Defenses Against DoS Attacks
1. Firewall Protection
Description
Filters incoming traffic.
📌 Blocks suspicious requests
2. Intrusion Detection/Prevention Systems (IDS/IPS)
Description
Detects and prevents malicious traffic.
3. Rate Limiting
Description
Limits number of requests per user.
📌 Prevents overload
4. Load Balancing
Description
Distributes traffic across multiple servers.
📌 Prevents single server overload
5. Traffic Filtering
Description
Blocks unwanted or malicious IP addresses.
6. Use of CDN (Content Delivery Network)
Description
Distributes traffic globally.
📌 Reduces attack impact
7. Blackholing and Sinkholing
Description
Redirects malicious traffic away from target.
8. Strong Network Design
Measures
- Redundant systems
- Backup servers
9. Monitoring and Logging
Description
Track unusual traffic patterns.
10. Anti-DDoS Services
Description
Specialized cloud-based protection services.
DoS Attacks and CIA Triad
- Confidentiality → Usually not affected
- Integrity → Not directly affected
- Availability → Major impact
📌 DoS primarily targets Availability.
DoS Attacks and Cyber Law (India)
Under IT Act, 2000:
- Section 43 → Damage/disruption of systems
- Section 66 → Cyber offences
📌 DoS attacks are punishable offences.
Advantages (Attacker Perspective)
- Easy to execute
- Can cause major disruption
- Hard to trace (in DDoS)
Disadvantages (Victim Perspective)
- Service downtime
- Financial loss
- Reputation damage
Conclusion
Denial-of-Service attacks are serious cyber threats that aim to disrupt system availability. Understanding their types and implementing strong defense mechanisms like firewalls, IDS, load balancing, and traffic filtering is essential to protect systems and ensure uninterrupted services.
📘 MCA Exam Tip
For 10–15 marks:
- Definition
- Types (Volume, Protocol, Application, DDoS)
- Working
- Defense techniques
- Example + conclusion