Database Encryption
Introduction
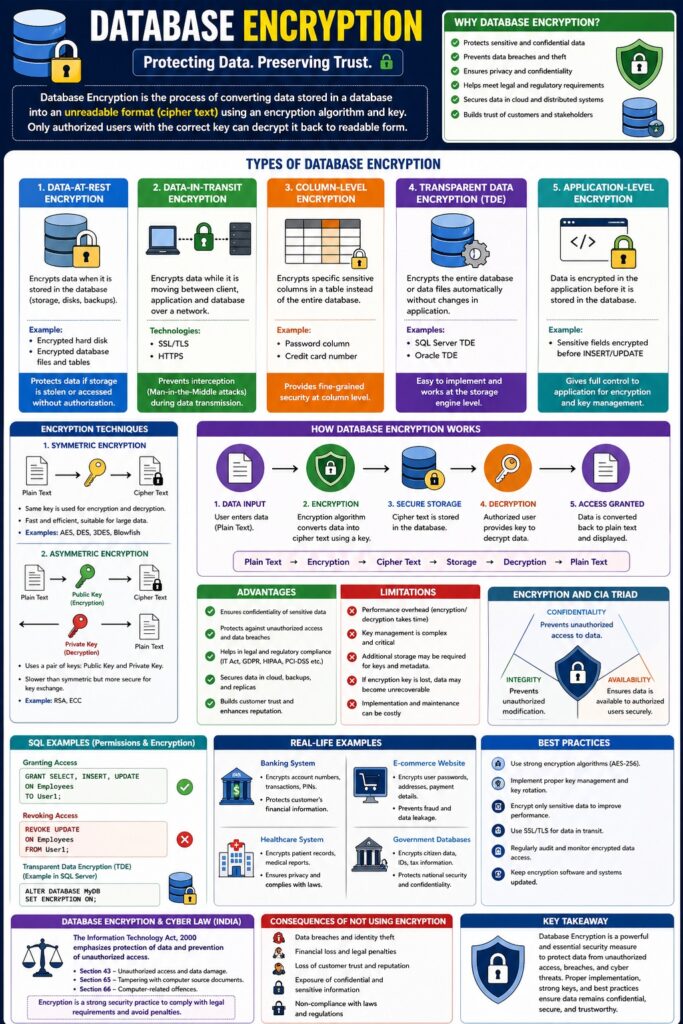
Database Encryption is a security technique used to protect data stored in a database by converting it into an unreadable format (cipher text). Only authorized users with the correct decryption key can convert it back into readable form (plain text).
👉 It is a critical part of database security and helps protect data from unauthorized access, breaches, and cyber attacks.
Meaning
Database encryption ensures that:
- Data is secure at rest (stored data)
- Data is secure in transit (during transmission)
📌 Even if attackers access the database, encrypted data remains unreadable.
Need for Database Encryption
- Protect sensitive data (banking, health records)
- Prevent data breaches
- Ensure privacy and confidentiality
- Meet legal and regulatory requirements
- Secure data in cloud environments
Types of Database Encryption
1. Data-at-Rest Encryption
Meaning
Encrypts data stored in the database.
Example
- Encrypted hard disk
- Encrypted database tables
📌 Protects data if storage is stolen or hacked.
2. Data-in-Transit Encryption
Meaning
Encrypts data while being transmitted over networks.
Technologies
- SSL/TLS
- HTTPS
📌 Prevents interception (Man-in-the-Middle attacks).
3. Column-Level Encryption
Meaning
Encrypts specific columns in a table.
Example
- Password column
- Credit card number
📌 Provides fine-grained security.
4. Transparent Data Encryption (TDE)
Meaning
Encrypts entire database automatically.
📌 No changes required in application.
Example
- SQL Server TDE
- Oracle TDE
5. Application-Level Encryption
Meaning
Data is encrypted before storing in database.
📌 Controlled by application logic.
Encryption Techniques Used
1. Symmetric Encryption
- Same key for encryption and decryption
- Fast and efficient
Examples:
- AES
- DES
2. Asymmetric Encryption
- Uses two keys:
- Public key
- Private key
Example:
- RSA
Working of Database Encryption
Step-by-Step Process
- Data is entered into system
- Encryption algorithm converts it into cipher text
- Data is stored securely in database
- Authorized user decrypts data when needed
Plain Text → Encryption → Cipher Text → Storage → Decryption → Plain Text
Advantages of Database Encryption
- Protects sensitive information
- Prevents unauthorized access
- Ensures confidentiality
- Helps in compliance with laws
- Secures cloud databases
Limitations
- Performance overhead
- Key management complexity
- Additional implementation cost
- Data recovery issues if key is lost
Database Encryption and CIA Triad
| CIA Component | Role |
|---|---|
| Confidentiality | Protects data from unauthorized access |
| Integrity | Prevents unauthorized modification |
| Availability | May affect performance but ensures secure access |
Database Encryption in Cyber Law (India)
Under IT Act, 2000:
- Protects against unauthorized access (Section 43)
- Prevents data misuse (Section 66)
📌 Encryption helps organizations follow reasonable security practices.
Real-Life Examples
Example 1: Banking System
- Encrypts account numbers and transactions
Example 2: E-commerce Website
- Encrypts user passwords and payment details
Best Practices for Database Encryption
- Use strong algorithms (AES-256)
- Secure key management
- Encrypt sensitive fields
- Use SSL/TLS for data transfer
- Regularly update encryption policies
Conclusion
Database Encryption is a powerful security mechanism that protects sensitive data from unauthorized access and cyber threats. By converting data into unreadable form, it ensures confidentiality and supports legal compliance. Proper implementation and key management are essential for effective database security.
📘 MCA Exam Tip
For 10–15 marks:
- Definition
- Types (at rest, in transit, column-level, TDE)
- Techniques (AES, RSA)
- Advantages + limitations
- Real-life examples