Database Access Control
Introduction
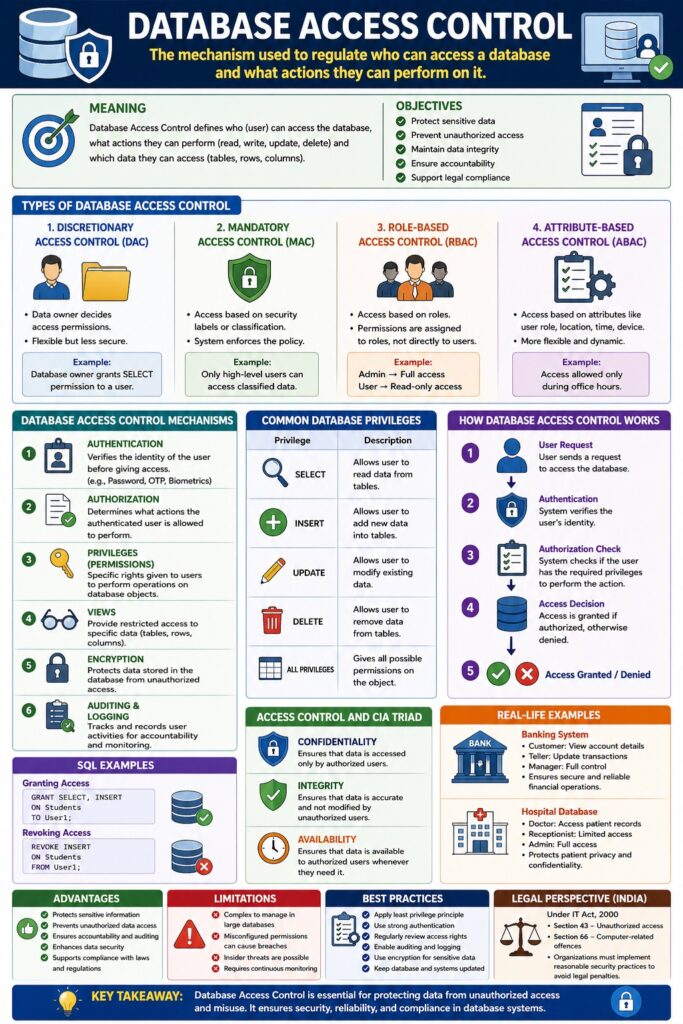
Database Access Control is the mechanism used to regulate who can access a database and what actions they can perform on it. It ensures that only authorized users can interact with database resources in a controlled and secure manner.
👉 It is a key component of database security and directly supports the CIA Triad (Confidentiality, Integrity, Availability).
Meaning
Database access control defines:
- Who (user/subject) can access the database
- What actions they can perform (read, write, update, delete)
- Which data they can access (tables, rows, columns)
📌 It prevents unauthorized access and misuse of data.
Objectives of Database Access Control
- Protect sensitive data
- Prevent unauthorized access
- Maintain data integrity
- Ensure accountability
- Support legal compliance
Types of Database Access Control
1. Discretionary Access Control (DAC)
Meaning
- Data owner decides access permissions
Example
Database owner grants SELECT permission to a user
2. Mandatory Access Control (MAC)
Meaning
- Access based on security labels (Confidential, Secret)
Example
Only high-level users can access classified data
3. Role-Based Access Control (RBAC)
Meaning
- Access based on roles
Example
- Admin → Full access
- User → Read-only access
4. Attribute-Based Access Control (ABAC) (Advanced)
Meaning
- Access based on attributes like:
- User role
- Location
- Time
Example
Access allowed only during office hours
Database Access Control Mechanisms
1. Authentication
Meaning
Verifies user identity
Methods
- Password
- OTP
- Biometrics
2. Authorization
Meaning
Defines what actions user can perform
3. Privileges (Permissions)
Common Database Privileges
- SELECT → Read data
- INSERT → Add data
- UPDATE → Modify data
- DELETE → Remove data
4. Views
Meaning
Provide restricted access to specific data
Example
User sees only limited columns of a table
5. Encryption
Meaning
Protects data stored in database
6. Auditing and Logging
Meaning
Tracks user activities
Example
Logs of database access and changes
Working of Database Access Control
Step-by-Step Process
- User sends request to database
- System authenticates user
- Authorization rules are checked
- Access is granted or denied
User → Authentication → Authorization → Access Granted / Denied
Database Access Control Models (SQL Example)
Granting Access
GRANT SELECT, INSERT ON Students TO User1;
Revoking Access
REVOKE INSERT ON Students FROM User1;
Advantages of Database Access Control
- Protects sensitive information
- Prevents unauthorized data access
- Ensures accountability
- Enhances data security
- Supports compliance
Limitations
- Complex management in large databases
- Misconfigured permissions can cause breaches
- Insider threats possible
Database Access Control and CIA Triad
| CIA Component | Role |
|---|---|
| Confidentiality | Restrict data access |
| Integrity | Prevent unauthorized changes |
| Availability | Ensure access for authorized users |
Real-Life Examples
Example 1: Banking System
- Customer → View account
- Teller → Update transactions
- Manager → Full control
Example 2: Hospital Database
- Doctor → Access patient records
- Receptionist → Limited access
- Admin → Full access
Database Access Control in Cyber Law (India)
Under IT Act, 2000:
- Section 43 → Unauthorized access
- Section 66 → Computer-related offences
📌 Organizations must implement proper controls to avoid legal penalties.
Best Practices
- Apply least privilege principle
- Use strong authentication
- Regularly review access rights
- Enable auditing and monitoring
- Use encryption
Conclusion
Database Access Control is a critical mechanism for protecting data from unauthorized access and misuse. By implementing proper authentication, authorization, and role-based permissions, organizations can ensure secure, reliable, and legally compliant database systems.
📘 MCA Exam Tip
For 10–15 marks:
- Definition
- Types (DAC, MAC, RBAC, ABAC)
- Mechanisms
- SQL example
- Advantages + examples