Data Encryption Standard (DES) – Detailed Explanation
Introduction
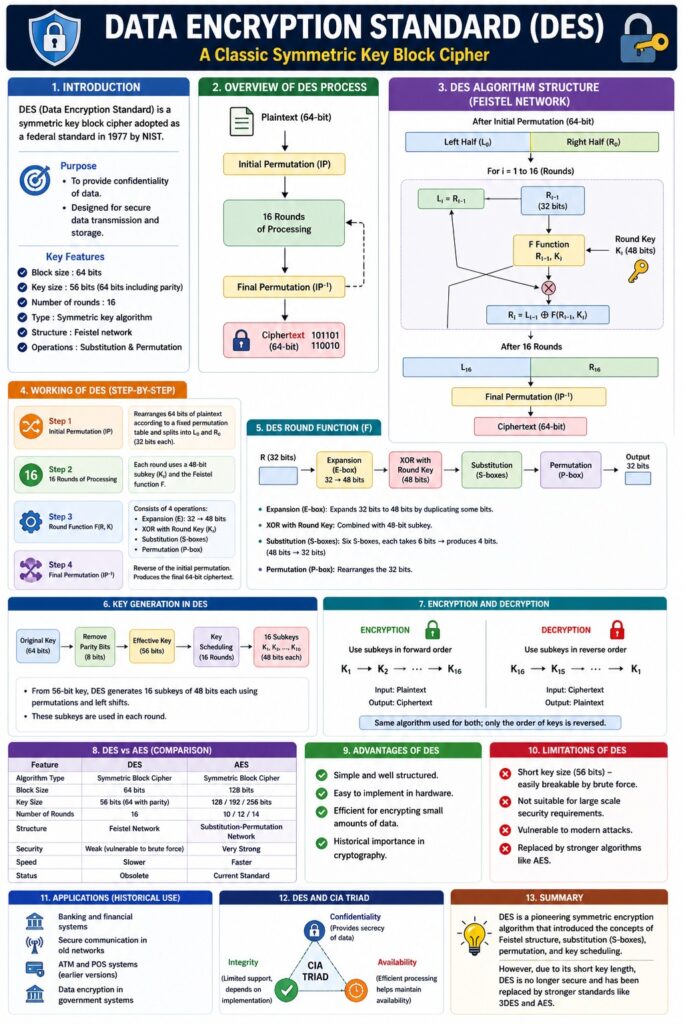
The Data Encryption Standard (DES) is a symmetric key block cipher used to encrypt data. It was adopted as a federal standard in 1977 by the National Institute of Standards and Technology.
👉 “DES = Classic symmetric encryption algorithm using a single secret key.”
Although historically important, DES is now considered insecure due to its short key length.
Definition
DES (Data Encryption Standard) is:
- A symmetric encryption algorithm
- That encrypts data in 64-bit blocks
- Using a 56-bit secret key
Key Features of DES
- Block size: 64 bits
- Key size: 56 bits (64 bits including parity)
- Number of rounds: 16
- Based on Feistel structure
- Uses substitution and permutation
Basic Structure of DES
DES follows a Feistel Network, where data is divided into two halves and processed through multiple rounds.
Plaintext (64-bit)
↓
Initial Permutation
↓
16 Rounds of Processing
↓
Final Permutation
↓
Ciphertext (64-bit)
Working of DES (Step-by-Step)
Step 1: Initial Permutation (IP)
- Rearranges bits of plaintext
- Produces two halves:
- Left (L0)
- Right (R0)
Step 2: 16 Rounds of Processing
Each round performs:
- Expansion of R (32 → 48 bits)
- XOR with round key
- Substitution using S-boxes
- Permutation (P-box)
- XOR with left half
📌 Output becomes input for next round
Step 3: Final Permutation (IP⁻¹)
- Reverse of initial permutation
- Produces final ciphertext
DES Round Function
L(i) = R(i-1)
R(i) = L(i-1) XOR F(R(i-1), K(i))
Where:
- F = Round function
- K(i) = Round key
Key Generation in DES
- Original key: 64 bits
- Effective key: 56 bits
- Generates 16 subkeys (48-bit each)
Encryption and Decryption
Encryption
- Uses keys in forward order (K1 → K16)
Decryption
- Uses keys in reverse order (K16 → K1)
📌 Same algorithm used for both
Advantages of DES
- Simple and well-structured
- Efficient in hardware implementation
- Historical importance
Limitations of DES
- Weak key size (56-bit)
- Vulnerable to brute-force attacks
- Outdated and insecure
- Replaced by stronger algorithms
Improvement: 3DES (Triple DES)
- Applies DES three times
- More secure than DES
DES vs AES
| Feature | DES | AES |
|---|---|---|
| Key Size | 56-bit | 128/192/256-bit |
| Security | Weak | Strong |
| Speed | Slower | Faster |
| Status | Obsolete | Standard |
Applications of DES (Historical)
- Banking systems
- Secure communications
- Early encryption systems
DES and CIA Triad
- Confidentiality → Encrypts data
- Integrity → Limited
- Availability → Efficient processing
Real-Life Example
- Early ATM encryption systems
- Secure data transmission in old networks
Conclusion
DES is a foundational symmetric encryption algorithm that introduced key concepts like Feistel structure, substitution, and permutation. However, due to its short key length and security vulnerabilities, it has been replaced by modern algorithms like AES. Despite this, DES remains important for understanding cryptographic principles.
📘 MCA Exam Tip
For 10–15 marks:
- Definition
- Structure (Feistel + 16 rounds)
- Working steps
- Diagram
- Advantages + limitations
- DES vs AES