Access Control: Access Control Principles
Introduction
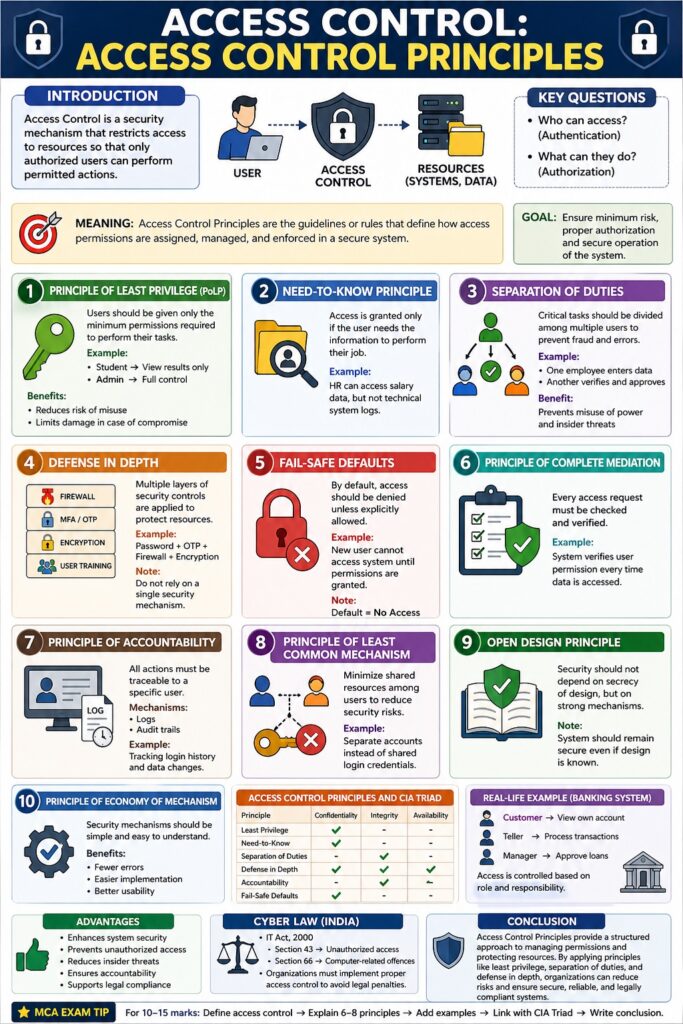
Access Control is a security mechanism that restricts access to resources (data, systems, networks) so that only authorized users can perform permitted actions.
👉 It answers two key questions:
- Who can access? (Authentication)
- What can they do? (Authorization)
Access control is essential to enforce the CIA Triad (Confidentiality, Integrity, Availability) and is widely used in operating systems, databases, and network security.
Meaning of Access Control Principles
Access Control Principles are the guidelines or rules that define how access permissions are assigned, managed, and enforced in a secure system.
These principles ensure:
- Minimum risk
- Proper authorization
- Secure system operation
Major Access Control Principles
1. Principle of Least Privilege (PoLP)
Meaning
Users should be given only the minimum permissions required to perform their tasks.
📌 “Give only what is necessary, nothing more.”
Example
- Student → View results only
- Admin → Full control
Benefits
- Reduces risk of misuse
- Limits damage in case of compromise
2. Need-to-Know Principle
Meaning
Access is granted only if the user needs the information to perform their job.
📌 Common in military and corporate environments.
Example
HR can access salary data, but not technical system logs.
3. Separation of Duties (SoD)
Meaning
Critical tasks should be divided among multiple users to prevent fraud and errors.
Example
- One employee enters data
- Another verifies and approves
Benefit
Prevents misuse of power and insider threats
4. Defense in Depth
Meaning
Multiple layers of security controls are applied to protect resources.
📌 “Do not rely on a single security mechanism.”
Example
- Password + OTP + Firewall + Encryption
5. Fail-Safe Defaults
Meaning
By default, access should be denied unless explicitly allowed.
📌 “Default = No Access”
Example
New user cannot access system until permissions are granted.
6. Principle of Complete Mediation
Meaning
Every access request must be checked and verified.
Example
System verifies user permission every time data is accessed.
7. Principle of Accountability
Meaning
All actions must be traceable to a specific user.
Mechanism
- Logs
- Audit trails
Example
Tracking login history and data changes
8. Principle of Least Common Mechanism
Meaning
Minimize shared resources among users to reduce security risks.
Example
Separate accounts instead of shared login credentials
9. Open Design Principle
Meaning
Security should not depend on secrecy of design, but on strong mechanisms.
📌 “System should remain secure even if design is known.”
10. Principle of Economy of Mechanism
Meaning
Security mechanisms should be simple and easy to understand.
Benefit
- Fewer errors
- Easier implementation
Access Control Principles and CIA Triad
| Principle | CIA Component |
|---|---|
| Least Privilege | Confidentiality |
| Need-to-Know | Confidentiality |
| Separation of Duties | Integrity |
| Defense in Depth | All (CIA) |
| Accountability | Integrity |
| Fail-Safe Defaults | Confidentiality |
Access Control in Cyber Law (India)
Under IT Act, 2000:
- Section 43 → Unauthorized access
- Section 66 → Computer-related offences
📌 Organizations must implement proper access control to avoid legal penalties.
Real-Life Example
In a banking system:
- Customer → View own account
- Teller → Process transactions
- Manager → Approve loans
Access is controlled based on role and responsibility.
Advantages of Access Control Principles
- Enhances system security
- Prevents unauthorized access
- Reduces insider threats
- Ensures accountability
- Supports legal compliance
Conclusion
Access Control Principles provide a structured approach to managing permissions and protecting resources. By applying principles like least privilege, separation of duties, and defense in depth, organizations can significantly reduce security risks and ensure secure, reliable, and legally compliant systems.