Security Issues in Servlets
Introduction
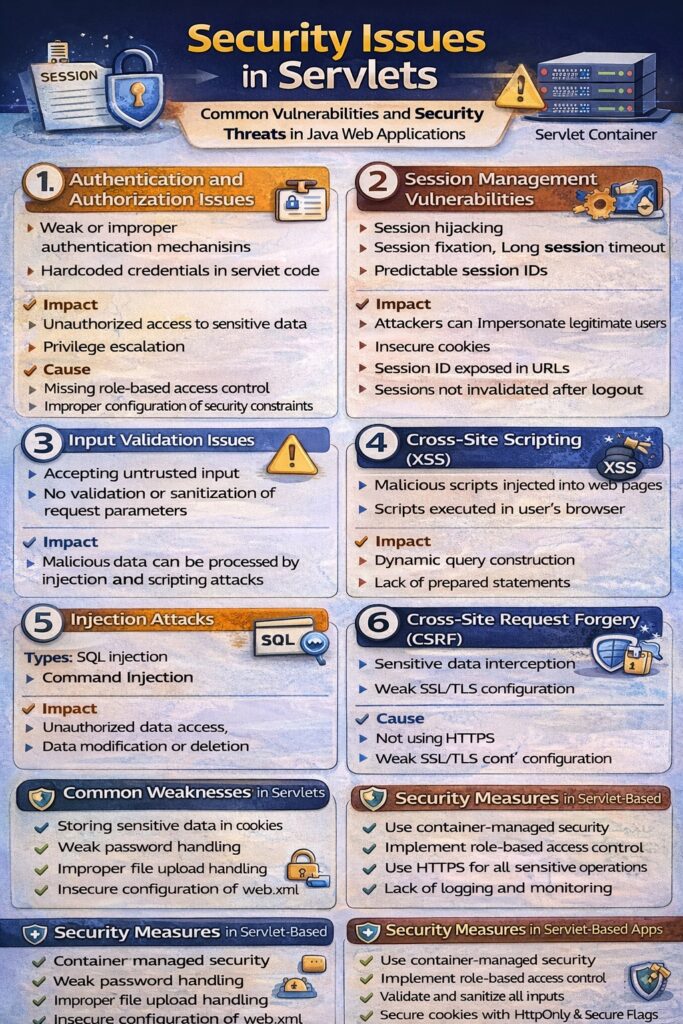
Servlets are widely used for developing server-side web applications. Since servlets handle client requests, sensitive data, sessions, and database interactions, they are exposed to various security threats. If not properly secured, servlet-based applications can become vulnerable to attacks that compromise confidentiality, integrity, and availability of data.
Understanding security issues in servlets is essential for building robust and secure web applications.
Major Security Issues in Servlets
Servlet security issues can be broadly categorized into the following areas:
- Authentication and Authorization Issues
- Session Management Vulnerabilities
- Input Validation Attacks
- Injection Attacks
- Cross-Site Scripting (XSS)
- Cross-Site Request Forgery (CSRF)
- Transport Layer Security Issues
- Improper Error Handling
1. Authentication and Authorization Issues
Problem
- Weak or improper authentication mechanisms
- Unauthorized users accessing restricted resources
- Hardcoded credentials in servlet code
Impact
- Unauthorized access to sensitive data
- Privilege escalation
Cause
- Missing role-based access control
- Improper configuration of security constraints
2. Session Management Vulnerabilities
Problem
- Session hijacking
- Session fixation
- Long session timeout
- Predictable session IDs
Impact
- Attackers can impersonate legitimate users
Cause
- Insecure cookies
- Session ID exposed in URLs
- Sessions not invalidated after logout
3. Input Validation Issues
Problem
- Accepting untrusted input from users
- No validation or sanitization of request parameters
Impact
- Malicious data can be processed by the server
- Leads to injection and scripting attacks
Cause
- Direct use of request parameters without validation
4. Injection Attacks
Types
- SQL Injection
- Command Injection
Problem
- User input directly used in database queries or system commands
Impact
- Unauthorized data access
- Data modification or deletion
- Database compromise
Cause
- Dynamic query construction
- Lack of prepared statements
5. Cross-Site Scripting (XSS)
Problem
- Malicious scripts injected into web pages
- Scripts executed in user’s browser
Impact
- Cookie theft
- Session hijacking
- Defacement of web pages
Cause
- Output not properly encoded
- Displaying user input directly in responses
6. Cross-Site Request Forgery (CSRF)
Problem
- Unauthorized actions performed on behalf of an authenticated user
Impact
- Data manipulation
- Unauthorized transactions
Cause
- No verification of request origin
- Missing CSRF tokens
7. Transport Layer Security Issues
Problem
- Data transmitted in plain text
- Insecure communication channels
Impact
- Sensitive data interception
- Man-in-the-middle attacks
Cause
- Not using HTTPS
- Weak SSL/TLS configuration
8. Improper Error Handling
Problem
- Displaying detailed error messages or stack traces
Impact
- Leakage of internal application details
- Easier exploitation by attackers
Cause
- No custom error pages
- Logging errors directly to client responses
General Security Weaknesses in Servlets
- Storing sensitive data in cookies
- Weak password handling
- Improper file upload handling
- Insecure configuration of web.xml
- Lack of logging and monitoring
Security Measures in Servlet-Based Applications
- Use container-managed security
- Implement role-based access control
- Use HTTPS for all sensitive operations
- Validate and sanitize all inputs
- Use prepared statements for database access
- Secure cookies with HttpOnly and Secure flags
- Proper session timeout and invalidation
- Handle errors gracefully using custom error pages
Conclusion
Security issues in servlets arise mainly due to improper handling of authentication, sessions, user input, and data transmission. Since servlets form the backbone of many Java web applications, securing them is critical to protect applications from common web attacks. By following secure coding practices and leveraging built-in servlet and container security features, developers can significantly reduce vulnerabilities and build reliable, secure web applications.
