Token-Based Authentication
Introduction
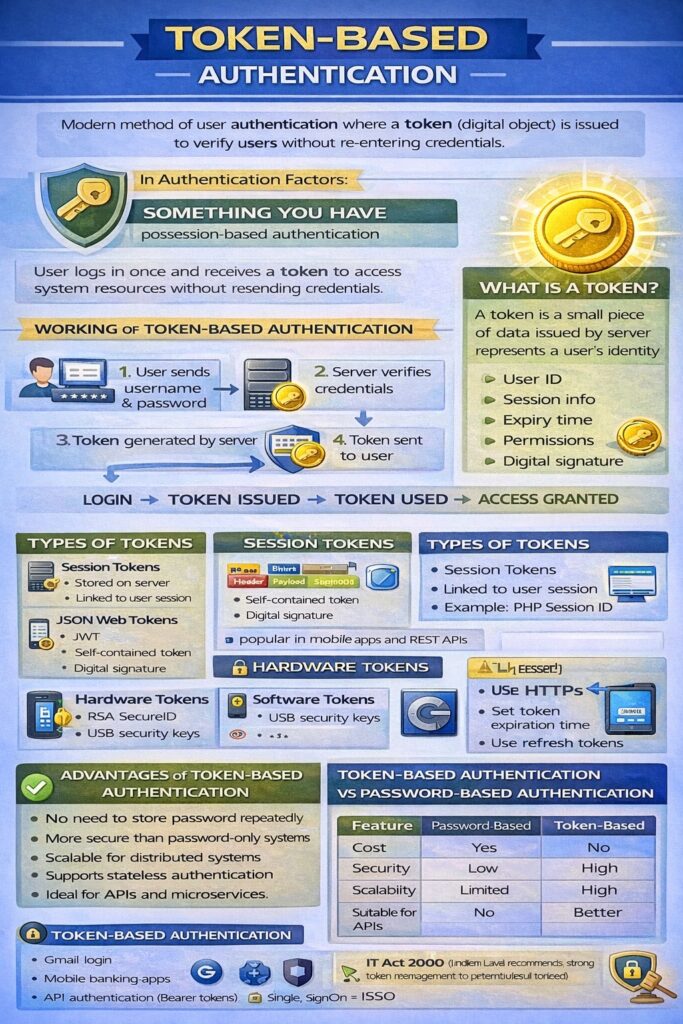
Token-Based Authentication is a modern authentication mechanism in which a token (a digital object or code) is issued to a user after successful login and is then used to access system resources without repeatedly entering credentials.
It belongs to the authentication factor:
👉 “Something You Have”
Token-based authentication is widely used in:
- Web applications
- APIs
- Cloud services
- Mobile apps
- Single Sign-On (SSO) systems
Meaning
In token-based authentication:
- The user authenticates once using credentials (username/password)
- The system generates a token
- The token is used for subsequent requests
- No need to resend username/password repeatedly
📌 Token proves that the user is already authenticated.
What is a Token?
A token is a small piece of data generated by the authentication server that represents the user’s identity and permissions.
Token may contain:
- User ID
- Session information
- Expiry time
- Permissions / roles
- Digital signature
Working of Token-Based Authentication
Step-by-Step Process
- User sends username & password to server
- Server verifies credentials
- Server generates a token
- Token is sent to the user
- User includes token in every request
- Server validates token and grants access
Login → Token Issued → Token Used → Access Granted
Types of Tokens
1. Session Tokens
- Stored on server
- Linked to user session
- Common in traditional web apps
Example: PHP session ID
2. JSON Web Tokens (JWT)
- Self-contained token
- Digitally signed
- Stored on client side
Structure of JWT:
- Header
- Payload
- Signature
📌 Very popular in REST APIs and mobile apps.
3. Hardware Tokens
- Physical devices
- Generate OTPs
Examples:
- RSA SecureID
- USB security keys
4. Software Tokens
- Mobile apps generate OTP
Examples:
- Google Authenticator
- Microsoft Authenticator
Advantages of Token-Based Authentication
- No need to store password repeatedly
- More secure than password-only systems
- Scalable for distributed systems
- Supports stateless authentication
- Ideal for APIs and microservices
Limitations / Challenges
- Token theft can lead to misuse
- Requires secure storage on client side
- Token expiration handling needed
- More complex than password-based systems
Token Security Measures
- Use HTTPS
- Set token expiration time
- Use refresh tokens
- Store tokens securely (not in plain text)
- Revoke tokens on logout
Token-Based Authentication vs Password-Based Authentication
| Feature | Password-Based | Token-Based |
|---|---|---|
| Credentials reuse | Yes | No |
| Security | Low | High |
| Scalability | Limited | High |
| Suitable for APIs | No | Yes |
| User experience | Medium | Better |
Token-Based Authentication and CIA Triad
- Confidentiality → Token replaces password
- Integrity → Digitally signed tokens
- Availability → Efficient session handling
Token-Based Authentication in Cyber Law (India)
Under IT Act, 2000:
- Section 3 & 3A → Electronic authentication
- Weak token management may cause unauthorized access (Section 43)
📌 Organizations must ensure reasonable security practices.
Real-Life Examples
- Login to Gmail → Token stored in browser
- Mobile banking apps
- Facebook / Instagram login
- API authentication using Bearer tokens
Comparison: Token vs OTP
- OTP → Short-lived, one-time use
- Token → Used for session duration
Conclusion
Token-based authentication is a secure, scalable, and efficient authentication mechanism widely used in modern applications. By eliminating repeated password transmission and using cryptographically protected tokens, it significantly improves system security and user experience. However, proper token management is essential to prevent misuse.
